Hacked businesses and organisations who paid huge ransoms to cybercriminals
A very curious cryptocurrency theft

Since February 2021, EU law enforcement agency Europol has arrested five members of REvil, a Russian cybercriminal gang also known as Sodinokibi. According to Reuters, REvil has made over $570 million (£425m) through ransomeware attacks. That's around $220 million (£164m) more than the total amount extorted in 2020. But although the world's law enforcers are cracking down on REvil, they're far from the only cybercriminals out there – and hackers have left businesses reeling all over the globe. From JBS to Colonial Pipeline, read on to see the big businesses and organisations that paid thousands, and even millions, to end a ransomeware attack.
Los Angeles Community College District: $28,000 (£20k)

Back in January 2017, the LA Community College District agreed to pay cybercrooks $28,000 (£20k) to end their hack of LA Valley College, which had encrypted files and disabled a slew of essential services and systems. Luckily, the college had taken out a cybercrime insurance policy that covered the cost of the ransom, and once paid the hackers provided a decryption key that allowed the institution to get its files back and network up and running again.
Hancock Health: $55,000 (£39k)

Along with education, healthcare is one of the sectors most targeted by ransomware gangs. In January 2018, Indiana hospital network Hancock Health had its systems breached and infected with virulent SamSam ransomware, which spread fast. The organisation ended up supplying four bitcoins, with a value of around $55,000 (£39k), in exchange for a decryption key, which thankfully worked. Most victims aren't so fortunate though; in fact, 92% of organisations that paid a ransom in the past year failed to get back all their data, with the average retrieving just 65%.
Sponsored Content
Park DuValle Community Health Center: $70,000 (£49k)

After it was hacked in June 2019, Park DuValle Community Heath Center in Louisville, Kentucky paid around $70,000 (£49k) in Bitcoin in order to recover 20,000 patient records that had been hacked. However, the attack actually cost the Center around $1 million (£706k) in total, with it paying $130,000 (£92k) to boost its system's cybersecurity alone.
Stratford, Ontario: $71,000 (£50k)

The city of Stratford in Ontario, Canada faced losing swathes of sensitive information forever when its systems were ravaged by a ransomware attack in April 2019. Against the advice of local law enforcement, the council negotiated with the hackers and ended the attack by parting with a Bitcoin payment of around $71,000 (£50k), most of which was covered by insurance. Interestingly, insurance companies have actually been accused of helping to fuel the explosion in this sort of cybercrime, since it's often in their interest to pay up instead of dealing with the fallout costs. The tide could be turning, however, with France's AXA the first insurance company to stop covering ransomware payments, in France at least.
NEO Urology: $75,000 (£53k)

Ohio healthcare provider NEO Urology had its entire system locked down in June 2019 by digital extortionists demanding $75,000 (£53k) in Bitcoin. Since it was losing up to $50,000 (£35k) each day the system was out of action, the organisation clearly felt it had no choice but to pay.
Sponsored Content
Uber: $100,000 (£71k)

La Porte County, Indiana: $130,000 (£92k)

Maastricht University: $220,000 (£155k)

Across the pond, Maastricht University in the Netherlands was targeted on Christmas Eve 2019 by Russian criminal gang TA505, who gained access after an employee inadvertently opened a phishing email a month before. The university opted to pay a ransom of 30 Bitcoin – worth $220,000 (£155k) at the time – to end the hack. Incidentally, the majority of ransomware attacks emanate from Russia, but China and North Korea are major hotspots as well.
Sponsored Content
Florence, Alabama: nearly $300,000 (£211k)
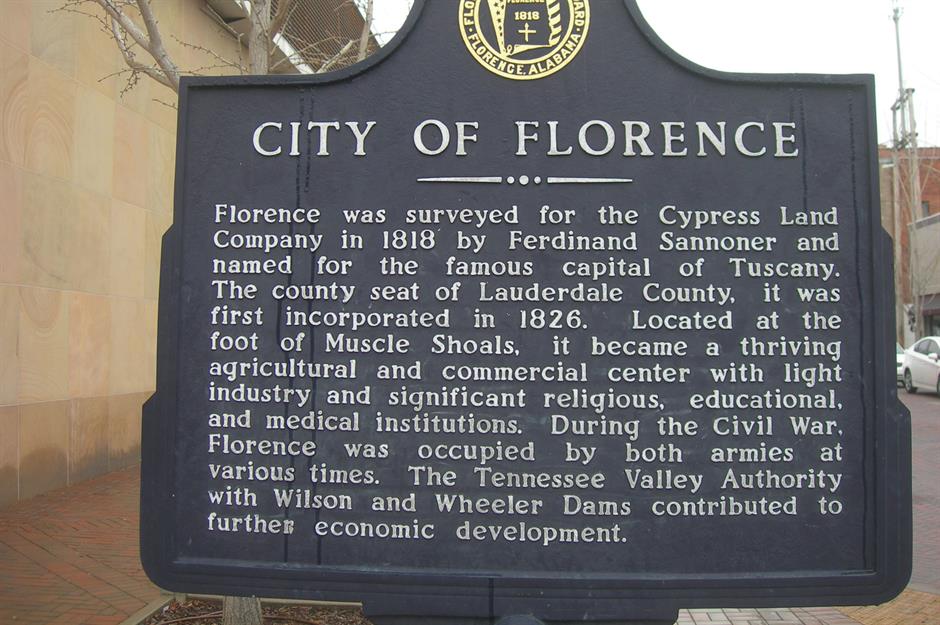
Cyberattacks increased last year as COVID-19 disruption and rushed working-from-home IT solutions left organisations vulnerable to data breaches. Last June, the city of Stratford in Alabama endured a double-extortion ransomware attack – the hackers not only disabled email but threatened to publish citizens' confidential information too. Outside negotiators were called in and the city eventually paid up a ransom of close to $300,000 (£211k) in Bitcoin, which was covered by insurance.
Tillamook County, Oregon: $300,000 (£211k)

Over in Oregon, Tillamook County was turned upside down in January 2020 when its IT and phone systems were disabled by hackers from Russian outfit Sodinokibi, aka REvil. Tillamook County caved but actually paid just under the going rate – the average ransomware payment stood at $312,493 (£220k) last year, up 171% from 2019.
Mystery Canadian company: $335,000 (£236k)

Sponsored Content
Cartersville, Georgia: $380,000 (£268k)

Jackson County, Georgia: $400,000 (£282k)

University of Utah: $457,059 (£322k)

The University of Utah endured a double extortion last July when hackers encrypted files and then threatened to leak them to the public. This double threat meant that the university paid the ransom even though it had back-ups. The attack is thought to have been carried out by the NetWalker gang, which had its servers confiscated and dark-web infrastructure shut down by the US Justice Department and Bulgarian authorities in January.
Sponsored Content
Delaware County, Pennsylvania: $500,000 (£352k)

CPI: $500,000 (£352k)

Lake City, Florida: $500,000 (£352k)

Sponsored Content
Riviera Beach City, Florida: $594,000 (£420k)

University Hospital, New Jersey $670,000 (£473k)

Last September, University Hospital in Newark was hacked by the SunCrypt gang, which may or may not be part of the Maze cartel. The gang harvested 240GB of data and leaked 1.7GB to scare the hospital into paying the $670,000 (£473k) ransom. Needless to say it duly obliged. SunCrypt later vowed never again to target a healthcare organisation but, worryingly, ransomware attacks on the sector are increasing, having spiked by 45% at the end of 2020.
Mystery Canadian insurance company: $950,000 (£670k)

In October 2019, an unnamed Canadian insurance company paid hackers 109.25 Bitcoin worth $950,000 (£670k) to end a major hack. The breach only came to light after the firm's English insurer tracked down a wallet containing the lion's share of stolen funds and launched a High Court bid to get it back. The case was successful and a judgement was made on 13 December 2019 granting the insurer an injunction to recover the Bitcoin, basically confirming the cryptocurrency's status as property.
Sponsored Content
Nayana: $1 million (£705k)

South Korean web hosting company Nayana suffered a calamitous ransomware attack in June 2017, which disabled 153 Linux servers and knocked out 3,400 customer websites. The firm negotiated with the hackers and managed to get the demand down from $4.4 million (£3.1m) to $500,000 (£352k), but the gang cruelly doubled it to $1 million (£705k) at the last minute. A record ransomware payout at the time, it hit the company hard and reportedly bankrupted the CEO.
UCSF: $1.14 million (£804k)

FatFace: $2 million (£1.45m)

In January this year UK fashion retailer FatFace's systems were hacked by a Conti ransomware gang. The hackers locked down the firm's computers and made off with 200GB of sensitive staff and customer data, which it threatened to publish for all to see. Like UCSF, FatFace brokered a deal with the crooks, and ended up paying $2 million (£1.45m) to stop the hack, having negotiated the figure down from $8 million (£5.7m).
Now read about the super-rich who want to pay more tax
Sponsored Content
Colonial Pipeline: $2.1 million (£1.5m)
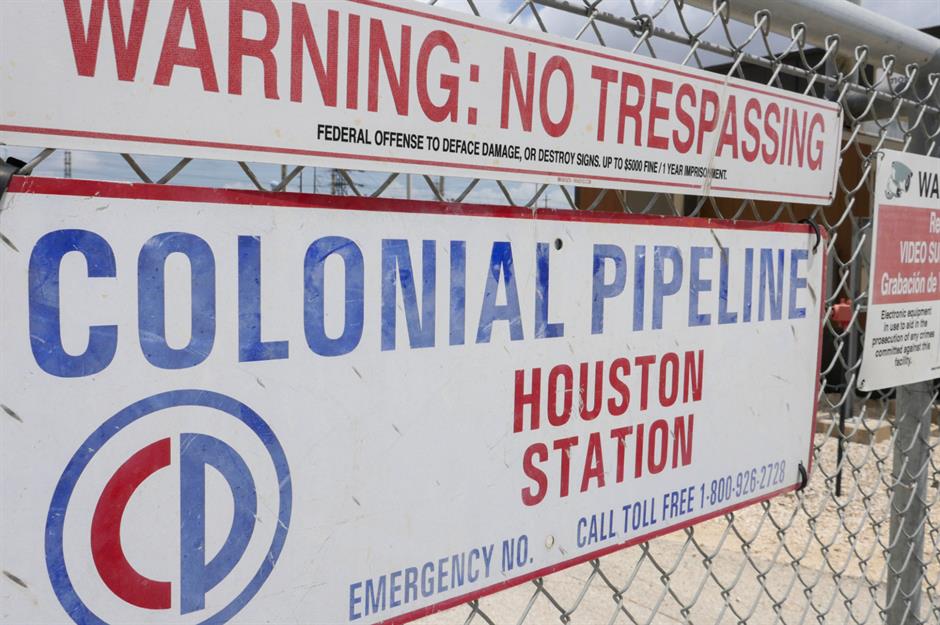
In May 2021, the Colonial Pipeline hack in America caused weeks of fuel shortages, and saw the organisation that delivers 45% of the East Coast's supply of petrol, diesel and jet fuel pay out $4.4 million (£3.1m) in cryptocurrency as a ransom to stop the attack. In exchange for the money the pipeline received a decryption tool to unlock its hacked system, but the tool was actually too slow and the Colonial Pipeline had to use its own back-ups to get the system back online. But in an almost unprecedented result, the FBI has since recovered $2.3 million (£1.6m) of the ransom from Russian gang DarkSide – thought to be made up of former associates of REvil – after it tracked the cryptocurrency payment and identified the virtual wallet the ransom was held in.
Travelex: $2.3 million (£1.6m)

One of REvil's earlier attacks came in 2019, when the gang struck gold by hacking UK-based foreign exchange company Travelex on New Year's Eve. The firm, which was dealt a double-extortion attack, agreed to give the hackers Bitcoin worth $2.3 million (£1.6m) to restore its systems and get confidential data wiped. Travelex collapsed into administration not long after, with the hack a major contributing factor in its demise.
Brenntag: $4.4 million (£3.1m)

Sponsored Content
CWT Global: $4.5 million (£3.2m)

Hackers using the Ragnar Locker strain of ransomware pocketed 414 Bitcoin worth $4.5 million (£3.2m) last July after stealing data and taking out 30,000 computers belonging to US travel management company GWT. Echoing other organisations in our round-up, the firm paid up after a tense negotiation – the perpetrators had originally asked for $10 million (£7.1m).
Mystery Austrian company: $4.9 million (£3.5m)

Garmin: $10 million (£7.1m)

US GPS device company Garmin was the victim of a hack last July that saw its global systems partly encrypted. The culprit was Russia's EvilCorp. Active since 2007, the gang favours the old school approach and, unlike the newer hacking groups, typically avoids double-extortion hacks, only encrypting files, rather than threatening to publish them. Still, the attack was crippling enough that Garmin agreed to pay the collective a $10 million (£7.1m) ransom.
Sponsored Content
JBS: $11 million (£7.8m)

In May, Brazilian meat processing company JBS saw its systems hacked, forcing the business to pause its operations in the US, Canada and Australia. In America, cattle slaughtering was stopped for a full day because of the attack. While not all of JBS's systems were affected, the company paid a ransom in Bitcoin to hackers worth $11 million (£7.8m) because of the sophistication of the attack. It later emerged the hackers were again part of the Russian group REvil.
Mystery company: $34 million (£24m)

According to cybersecurity expert Vitali Kremez, a major company paid a gang that had used Ryuk ransomware to infect its systems $34 million (£24m) for the decryption key that ended the attack. This would make it the largest ransomware payout by a long shot. But with cybercrime on the up, this record nobody wants is likely to be beaten soon.
Now read: Biden lifts the sanctions on this controversial Russian megaproject
Comments
Be the first to comment
Do you want to comment on this article? You need to be signed in for this feature